Mobile device management: Difference between revisions
→Remote Application Management tools: section removed |
|||
| Line 80: | Line 80: | ||
Similarly, the iOS App Store app can be typically chosen from the list. It’s a bit more complicated in the case of custom mobile apps because line-of-business distribution on iOS requires resigning the resulting app with your Apple Developer distribution certificate (see [[Enterprise deployment on iOS]]). | Similarly, the iOS App Store app can be typically chosen from the list. It’s a bit more complicated in the case of custom mobile apps because line-of-business distribution on iOS requires resigning the resulting app with your Apple Developer distribution certificate (see [[Enterprise deployment on iOS]]). | ||
=== Integrating custom iOS app with Microsoft Intune === | |||
Microsoft provides the [https://learn.microsoft.com/en-us/mem/intune/developer/app-wrapper-prepare-ios MS Intune App Wrapping Tool] for injecting security features into existing IPA installation. Here is the digest of the MS Intune documentation: | |||
Prerequisites: | |||
* Mac OS 12.6 or later with Xcode 13.x (v14.x won’t work!) | |||
* Apple Developer account with a valid distribution certificate, App ID for bundle ID (package name) of your custom app, In-house provisioning profile for this App ID (AdHoc can also be used, but it requires app resigning after adding a new device into the team). | |||
Steps: | |||
# Request the build of your [[custom mobile apps|custom mobile app]] via Woodford. | |||
# Your Resco account manager contacts you to discuss the pricing and approves the build. | |||
# Our branding portal makes the new IPA installation based on your mobile app request. You obtain a download link by email. Download the IPA file. | |||
# Make sure that you have a distribution certificate with the private key on your Mac. Type the following command to Terminal: | |||
#: <code>Security find-identity -v -c codesigning</code> | |||
# Copy certificate hash into clipboard | |||
# Download provisioning profile for your app and place it into same folder as IPA. | |||
# Download the [https://github.com/msintuneappsdk/intune-app-wrapping-tool-ios/archive/refs/tags/16.1.1.zip MS Intune App Wrapping Tool v16.1.1] (v17.x won’t work!), unzip it, mount included DMG file and copy “IntuneMAMPackager” folder into ~/Applications. | |||
# Open Terminal app, go to folder with IPA and place following command (replace MobileCrm.ipa with real file name and [CertificateHash] with hash from clipboard): | |||
#: <code>~/Applications/IntuneMAMPackager/Contents/MacOS/IntuneMAMPackager -i MobileCrm.ipa -o MobileCrm-wrapped.ipa -p MobileCrmInHouse.mobileprovision -c [CertificateHash] -v true</code> | |||
# Upload MobileCrm-wrapped IPA into Microsoft EndPoint Manager as line-of-business app | |||
=== Integrating custom iOS app with Citrix XenMobile === | |||
Citrix provides [https://github.com/citrix/citrix-mam-sdks MAM SDK] implementing security features in apps. SDK isn’t part of our App Store app, but it can be incorporated into [[custom mobile apps]]. Make sure to enable '''Include Citrix MAM SDK''' before requesting a new custom app build. If you also provided a valid distribution certificate and provisioning profile, the resulting IPA installation should be suitable for side-loading onto your devices. Otherwise, you must resign the IPA with your certificate and provisioning profile (see [[Enterprise deployment on iOS]]). | |||
However, Citrix EndPoint Management doesn’t support IPA installation, and it requires a wrapped MDX envelope. To achieve it, you must pass the following steps: | |||
Prerequisites: | |||
* Mac OS 12.6 or later with Xcode 13+ | |||
* Citrix MAMSDK_iOS.zip file from GitHub releases | |||
Steps: | |||
# Request the build of your [[custom mobile apps|custom mobile app]] via Woodford. | |||
# Your Resco account manager contacts you to discuss the pricing and approves the build. | |||
# Our branding portal makes the new IPA installation based on your mobile app request. You obtain a download link by email. Download the IPA file. | |||
# If you haven’t provided the distribution certificate and provisioning profile into the Mobile Apps config, resign the IPA file with your distribution certificate (see [[Enterprise deployment on iOS]]). | |||
# Unpack the MAM SDK and copy MobileCrm.ipa file into the SDK root folder. | |||
# Download the [https://www.resco.net/downloads/CitrixMdxGenerator.zip MDX generator script] and unpack it into the same folder. | |||
# Open the Terminal app, go to the MAM SDK root folder (command <code>cd [folderpath]</code>), and enter the following command:<br><code>./generate_mdx MobileCrm.ipa</code> | |||
# Upload the MobileCrm_Full.mdx file into [https://docs.citrix.com/en-us/citrix-endpoint-management/apps.html#add-an-mdx-app Citrix EndPoint Management] and configure specific app details and policy settings that the [https://docs.citrix.com/en-us/mdx-toolkit/mam-sdk-policies-ios.html Endpoint Management Store] enforces. | |||
Revision as of 06:53, 28 September 2022
Mobile device management (MDM) is the administration of mobile devices, such as smartphones, tablet computers and laptops.
Built-in features
Resco platform includes some traditional MDM features out of the box. The backend administrator can access the list of connected mobile devices, assign different security policies to users, remotely control/synchronize/wipe app from user device, and much more. See Enterprise security for more information.
Third-party MDM providers
Resco Mobile CRM app can be managed by MDM providers, such as Microsoft Intune, Citrix Xen Mobile or Google Enterprise Distribution. Our App Store / Play Store app can be used for MDM distribution with limited support of security features (see the Security section below). More advanced MDM integration requires requesting a custom mobile app with MDM integration.
MDM admins can control which version of Resco app is installed on the managed devices, or even restrict certain features of our app. However, Resco apps require a set of permissions for their function, too strict control can break the app.
MDM also adds another layer to the complexity of the update and change management. See best practices for upgrading Resco apps for more information.
Essentially, there are two main scenarios for MDM:
- Distribution
- Security
App distribution
The main motivators for centralized distribution are:
- manage the version that users have installed
- block access to the app store for security reasons
For example, if you have a custom JavaScript solution that you have meticulously tested with a certain version of the app or a finetuned custom integration solution, you might decide to skip some releases so that you don't have to test everything anew. However, in order to be eligible for Resco support, you need to update your app at least once a year. Also, the operating systems on mobile devices should be kept up to date at least once a year.
If you want to use MDM for centralized distribution of the app on a larger number of devices, this should not be a problem. To this date, the Resco support team has been able to help with any requested MDM solution. In this scenario, the MDM provider should request a custom version of the Resco app, either as an IPA file (iOS) or APK/AAB file (Android). Resco support will provide a version of the app ready to be signed by the customer's provisioning profile and certificate. In the case of Custom Mobile App, you have full control over requesting the new version, and you’ll be served by our semi-automated build system.
We have received reports from our customers, that in the case of iOS, many have successfully used the app store version of the app for distribution - no need for a custom installation file from Resco. However, we are happy to provide such custom files if needed. Contact Resco support for more information.
Security
In the case of security, the situation can be more complicated. The common use cases for security features of MDM include:
- Using app-specific configuration (key-value pairs) for prefilling URL, name, etc. See App-specific configuration support section.
- Setting up Exchange or SharePoint access
- Restricting the communication between the managed Resco app and non-managed apps
- App-specific restrictions blocking features like copy/paste, taking screenshots, enforcing encryption, and much more
- Initiating a private VPN to access protected enterprise resources
- Enabling conditional access to enterprise resources
| Warning | Keep in mind that if you block email clients, the app cannot send a log file to the support email address. |
Enabling security features varies across different MDM providers and platforms. Some of them (e.g., Citrix on iOS or MS Intune on Android) require Mobile Application Management (MAM) SDK to be included in the app, while others (e.g., MS Intune on iOS) provide wrapping tools that take app installation (IPA / APK / AAB) and inject protection layer on a binary level. Some of the scenarios are described below.
MDM support on iOS
iOS has support for MDM systems incorporated in the operating system. Some of the security features are supported out-of-the-box, even for apps having no specific MDM support. Here is the list of supported security features for specific MDM providers:
| Feature | Microsoft Intune | Citrix Xen Mobile | Other MDMs |
|---|---|---|---|
| Deployment | AppStore app & custom apps | AppStore app & custom apps | AppStore app & custom apps |
| App-specific configuration | AppStore app & custom apps | AppStore app & custom apps | AppStore app & custom apps |
| App-specific restrictions | Custom app wrapped with Intune App Wrapping Tool | Custom app with Citrix MAM SDK | No support |
| Private VPN support and CA | Custom app wrapped with Intune App Wrapping Tool | Custom app with Citrix MAM SDK | No support |
MDM support on Android
Currently, we support only Microsoft Intune and Google Enterprise Distribution on Android. Google Enterprise Distribution is supported without any requirements for the app: even the Google Play store version can be used. Microsoft Intune support requires a custom-built mobile app with MS Intune MAM SDK opted in.
Integrating the Android app with MDM is straightforward. You can typically choose the Play Store app from the list. In the case of custom mobile apps, choose the “Line-of-business app” option and upload the APK installation produced by our branding process.
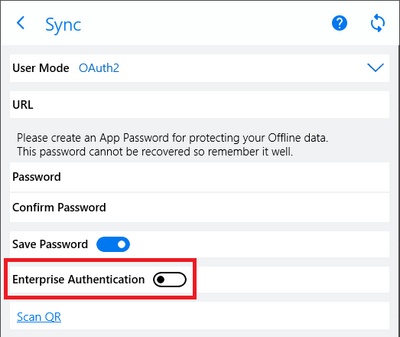
Use enterprise authentication on Windows apps
If you want to use authentication methods like conditional access, user certificates, or reverse proxy on Windows Desktop and Windows Store (UWP) apps, the mobile user needs to enable the Enterprise Authentication switch in the Sync window.
This option delegates the OAuth2 authentication flow to the default browser (which must be managed) and gets the authentication result back to the application using the app's URL scheme. Users might experience a confirmation dialog after successful login and they must confirm redirection to our app to deliver the result back to the synchronization dialog.
Integrating app with MDM
Integrating the Android app with MDM is straightforward. You can typically choose Play Store app from the list. In the case of custom mobile apps, choose “Line-of-business app” option and upload the APK installation produced by our branding process.
Similarly, the iOS App Store app can be typically chosen from the list. It’s a bit more complicated in the case of custom mobile apps because line-of-business distribution on iOS requires resigning the resulting app with your Apple Developer distribution certificate (see Enterprise deployment on iOS).
Integrating custom iOS app with Microsoft Intune
Microsoft provides the MS Intune App Wrapping Tool for injecting security features into existing IPA installation. Here is the digest of the MS Intune documentation:
Prerequisites:
- Mac OS 12.6 or later with Xcode 13.x (v14.x won’t work!)
- Apple Developer account with a valid distribution certificate, App ID for bundle ID (package name) of your custom app, In-house provisioning profile for this App ID (AdHoc can also be used, but it requires app resigning after adding a new device into the team).
Steps:
- Request the build of your custom mobile app via Woodford.
- Your Resco account manager contacts you to discuss the pricing and approves the build.
- Our branding portal makes the new IPA installation based on your mobile app request. You obtain a download link by email. Download the IPA file.
- Make sure that you have a distribution certificate with the private key on your Mac. Type the following command to Terminal:
Security find-identity -v -c codesigning
- Copy certificate hash into clipboard
- Download provisioning profile for your app and place it into same folder as IPA.
- Download the MS Intune App Wrapping Tool v16.1.1 (v17.x won’t work!), unzip it, mount included DMG file and copy “IntuneMAMPackager” folder into ~/Applications.
- Open Terminal app, go to folder with IPA and place following command (replace MobileCrm.ipa with real file name and [CertificateHash] with hash from clipboard):
~/Applications/IntuneMAMPackager/Contents/MacOS/IntuneMAMPackager -i MobileCrm.ipa -o MobileCrm-wrapped.ipa -p MobileCrmInHouse.mobileprovision -c [CertificateHash] -v true
- Upload MobileCrm-wrapped IPA into Microsoft EndPoint Manager as line-of-business app
Integrating custom iOS app with Citrix XenMobile
Citrix provides MAM SDK implementing security features in apps. SDK isn’t part of our App Store app, but it can be incorporated into custom mobile apps. Make sure to enable Include Citrix MAM SDK before requesting a new custom app build. If you also provided a valid distribution certificate and provisioning profile, the resulting IPA installation should be suitable for side-loading onto your devices. Otherwise, you must resign the IPA with your certificate and provisioning profile (see Enterprise deployment on iOS).
However, Citrix EndPoint Management doesn’t support IPA installation, and it requires a wrapped MDX envelope. To achieve it, you must pass the following steps:
Prerequisites:
- Mac OS 12.6 or later with Xcode 13+
- Citrix MAMSDK_iOS.zip file from GitHub releases
Steps:
- Request the build of your custom mobile app via Woodford.
- Your Resco account manager contacts you to discuss the pricing and approves the build.
- Our branding portal makes the new IPA installation based on your mobile app request. You obtain a download link by email. Download the IPA file.
- If you haven’t provided the distribution certificate and provisioning profile into the Mobile Apps config, resign the IPA file with your distribution certificate (see Enterprise deployment on iOS).
- Unpack the MAM SDK and copy MobileCrm.ipa file into the SDK root folder.
- Download the MDX generator script and unpack it into the same folder.
- Open the Terminal app, go to the MAM SDK root folder (command
cd [folderpath]), and enter the following command:./generate_mdx MobileCrm.ipa - Upload the MobileCrm_Full.mdx file into Citrix EndPoint Management and configure specific app details and policy settings that the Endpoint Management Store enforces.